EMF-REST: Your models on the web via a RESTful API
EMF-REST generates truly RESTful APIs for your EMF models. EMF-REST complements the existing (Java-based) API generation facilities EMF already provides and extends them to the Web.
EMF-REST generates truly RESTful APIs for your EMF models. EMF-REST complements the existing (Java-based) API generation facilities EMF already provides and extends them to the Web.
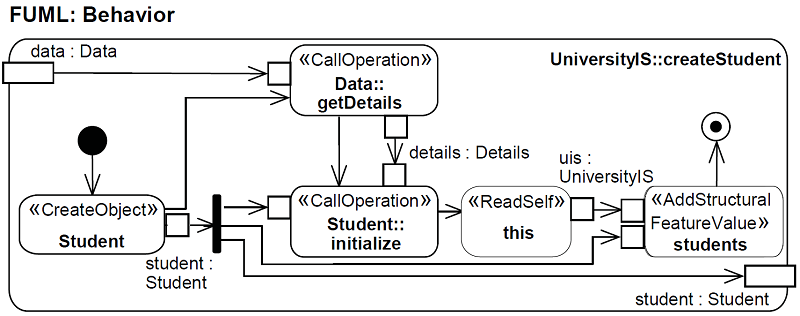
fREX is an open framework for reverse engineering of executable behaviors from existing software code bases (currently Java is supported) using fUML as a pivot language
Definition of security policies is perceived as an important activity by developers, but at the same time they say it’s complex and error prone. Read the full results
Help us (the researchers) to help you by answering this survey so that we can then target our security analysis algorithms to what you need!
Create random models to test your modeling tools. Make them as large as you need them to be. It uses uniform probability distributions to populate.
Recent Comments