
by Salvador Martínez | Sep 17, 2018 | article, architecture, DSLs, security
Read about our access-control mechanisms for models. We rely on a new domain-specific language tailored to the definition of RBAC rules on models and on its enforcement thanks to the automatic generation of security compliant (virtual) views.

by Javier Cánovas | Jul 2, 2018 | article, security
A common problem when modeling software systems is the lack of support to specify how to enforce privacy concerns in data models. In this post, we propose a profile to define and enforce privacy concerns in UML class diagrams. Models annotated with our profile can be used in model-driven methodologies to generate privacy-aware applications.
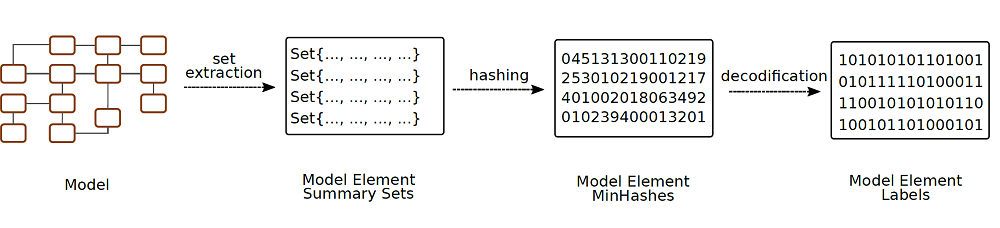
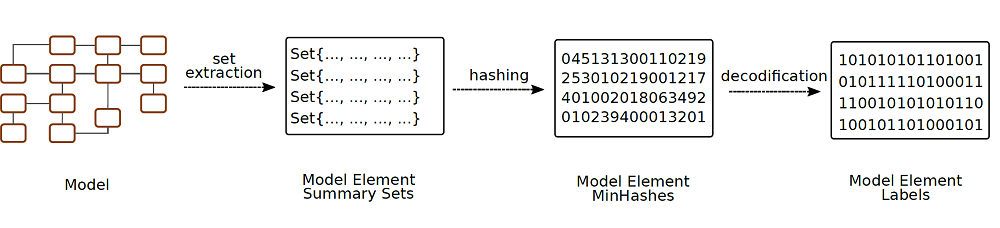
by Salvador Martínez | May 29, 2018 | article, security
We propose the integration of digital watermarking techniques in the model-driven engineering development lifecycle as way to protect the intellectual property of your modeling artefacts in collaborative modeling scenarios
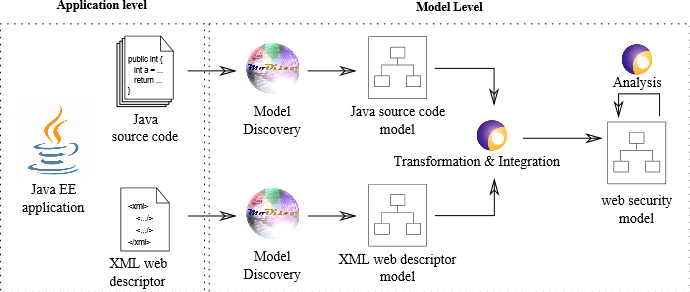
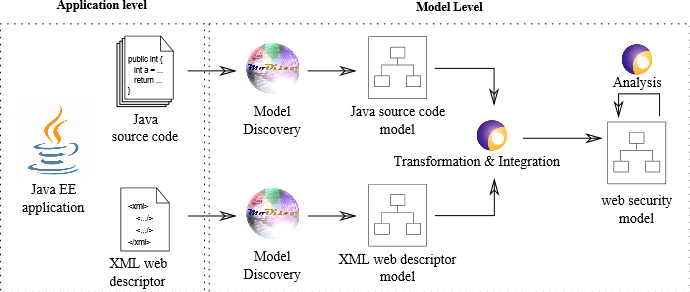
by Jordi Cabot | Feb 21, 2017 | article, cloud & web engineering, security
Our work helps security experts to visualize, (automatically) analyse and manipulate web security access-control policies, specially for Java EE
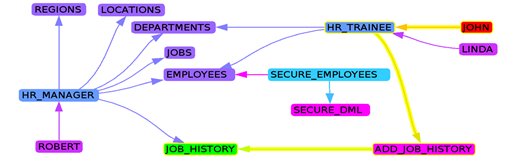
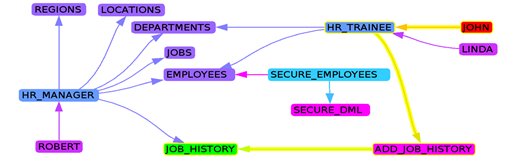
by Jordi Cabot | Dec 14, 2016 | databases, reverse engineering, security
Automatic extraction of security policies that generates an RBAC security model from an existing database by analyzing its dictionary, views, triggers,…

by Jordi Cabot | Nov 4, 2016 | article, security
Have you ever thought about using model transformations to specify and enforce access-control policies? Check how we do it




Recent Comments